Professional Services for Security Solutions

Strategic Security Consulting
Cyberium’s Strategic Security Consulting service delivers expert guidance and comprehensive planning to help organizations build resilient cybersecurity programs that align deeply with business objectives and risk landscapes. Our consultants work closely with clients to conduct thorough risk assessments, vulnerability analyses, and gap evaluations that uncover critical security weaknesses and compliance shortfalls. Using this insight, Cyberium crafts detailed, prioritized security roadmaps that address immediate threats while planning for long-term resilience.
Benefits
- Comprehensive Risk Insight
- Business-Aligned Roadmaps
- Regulatory Preparedness
Questions? You’re covered
What is strategic security consulting?
Why is risk assessment important in security consulting?
It identifies vulnerabilities and threats, enabling prioritized, effective mitigation strategies to protect key assets.
How does Cyberium tailor security strategies to business needs?
What role does governance play in strategic security consulting?
Governance establishes policies, accountability, and processes that embed security into the corporate culture and operations.
How often should security strategies be reviewed and updated?

Secure Architecture Design & Implementation
Cyberium’s Secure Architecture Design & Implementation service provides expert planning, development, and deployment of robust cybersecurity infrastructures tailored to an organization’s unique needs and risk profile. Our team designs scalable and resilient security architectures that protect critical assets across cloud, on-premises, and hybrid environments. We emphasize integrating modern security frameworks including zero trust, micro-segmentation, identity and access management, and encryption technologies to build comprehensive defense-in-depth.
Benefits
- Tailored Security Frameworks
- Seamless Integration
- Scalable & Resilient
Questions? You’re covered
What is secure architecture design in cybersecurity?
It involves creating tailored, multi-layered security frameworks that protect organizational assets across all IT environments.
How does Cyberium ensure smooth implementation of security architectures?
Through thorough planning, technology compatibility assessments, and close collaboration with client teams to avoid operational disruption.
What types of security frameworks does Cyberium implement?
Cyberium implements zero trust, micro-segmentation, identity management, encryption, and other modern security frameworks.
Why is scalability important in security architecture?
Scalability ensures that security infrastructures can grow with business expansion and adapt to emerging threats effectively.
How does continuous support enhance secure architecture?
Ongoing monitoring and iterative improvements keep security defenses up-to-date and aligned with evolving risk environments.
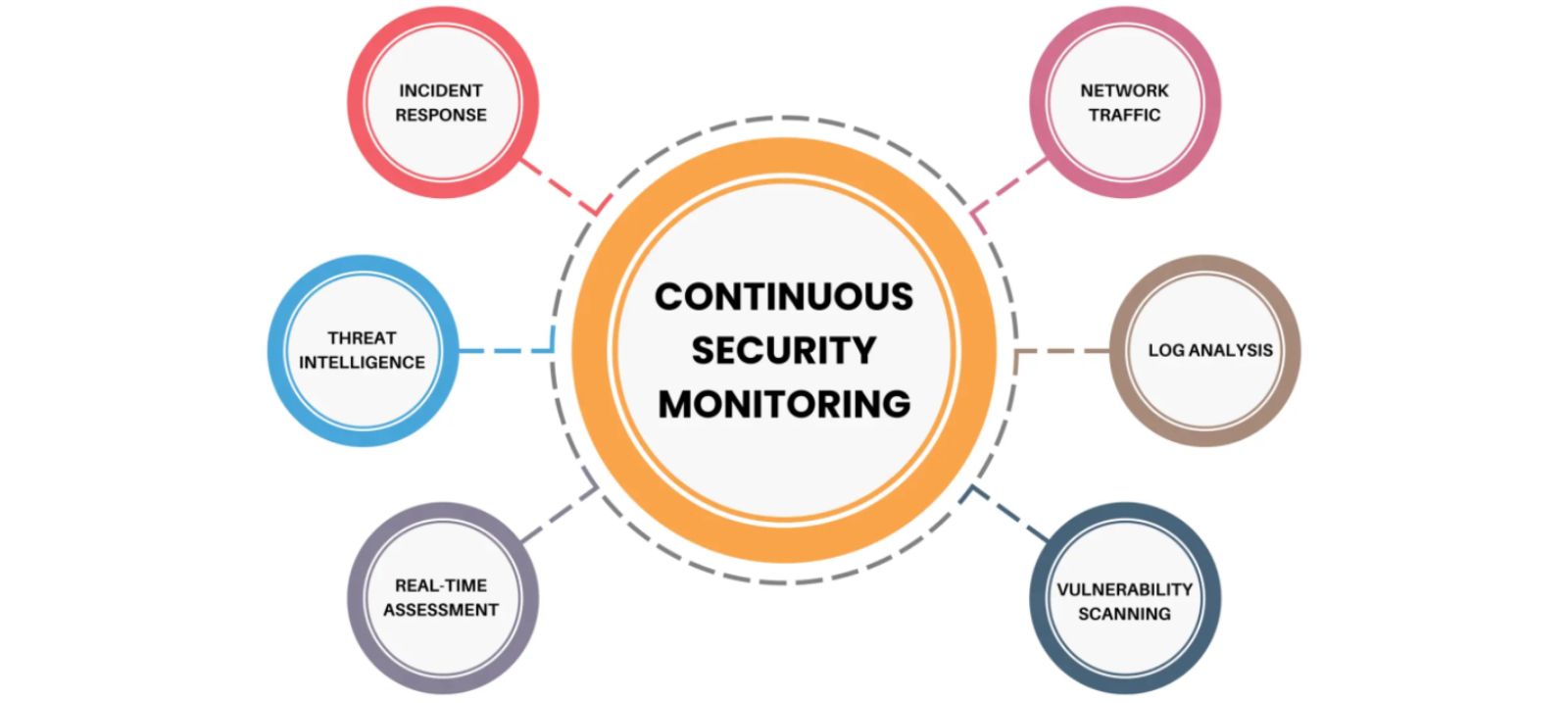
Continuous Monitoring & Incident Response
Cyberium’s Continuous Monitoring & Incident Response service provides comprehensive, real-time surveillance of your IT infrastructure combined with rapid reaction capabilities to detect, analyze, and mitigate cybersecurity threats. Our experts leverage advanced security information and event management (SIEM) platforms, threat intelligence feeds, and machine learning-powered analytics to continuously monitor network traffic, system logs, and user behaviors across your entire digital environment.
Benefits
- 24/7 Threat Detection
- Rapid Incident Handling
- Regulatory Compliance
Questions? You’re covered
What is continuous security monitoring?
It involves constant observation of IT environments to detect and respond to cyber threats in real time.
How does Cyberium respond to security incidents?
Cyberium uses predefined response playbooks and expert teams to rapidly contain and mitigate threats.
Why is continuous monitoring important for cybersecurity?

Compliance & Governance Enablement
Cyberium’s Compliance & Governance Enablement service helps organizations navigate complex regulatory landscapes by embedding governance frameworks and compliance requirements directly into cybersecurity strategies. Our experts work closely with your legal, IT, and operational teams to develop and implement policies, controls, and processes that align with global standards such as ISO 27001, GDPR, HIPAA, PCI DSS, and SOC 2.
Benefits
- Regulatory Alignment
- Risk Reduction
- Operational Integration
- Agility & Adaptability
Questions? You’re covered
What is compliance and governance enablement in cybersecurity?
It’s the process of embedding regulatory and governance requirements into cybersecurity frameworks and business operations.